Lao Gao talks about "Bybit theft and North Korean hackers": The transaction address is garbled and difficult to identify, and it is to blame that the multi-signature personnel did not confirm it
Well-known YouTuber Lao Gao released a video yesterday to analyze the Bybit theft incident, saying that hackers penetrated Bybit's multi-signature mechanism through social engineering and successfully defrauded the authorization of three signatories. However, these three signatories actually had ways to avoid this unfortunate incident. However, security experts said that part of Lao Gao's interpretation may be wrong.
(Preliminary summary: All 500,000 ETH stolen from Bybit were washed away as hidden selling pressure? The CEO issued an announcement to clarify: 77% of the cash flow can be traced)
(Background supplement: Bybit CEO personally recounted the 72 hours of life and death: the chief financial officer tremblingly said that he lost 410,000 ETH and had an internal P-1 emergency mechanism...)
The cryptocurrency exchange Bybit was attacked by hackers on the 21st of last month. About US$1.5 billion in ETH was stolen from Bybit's cold wallet, becoming the largest theft in the history of the cryptocurrency industry. The North Korean hacker group "Lazarus Group" is believed to be behind the hacking attack.
Lao Gao talks about the Bybit theft incident
The well-known YouTuber Lao Gao released a video yesterday to analyze the Bybit theft incident and the Lazarus Group. He pointed out that Bybit's cold wallet uses a multi-signature mechanism, which requires three persons in charge to sign in order to unlock the funds, which is theoretically extremely safe.
However, Lao Gao pointed out that the hackers targeted the first signer and implanted malware into his device through social engineering. When the employee opened the transaction interface, it seemed nothing unusual, but in fact "the interface of this bank account is fake." The transfer information has been modified. He completed the signature without realizing it. Then the second and third people signed without noticing the abnormality, resulting in the wallet being stolen:
Once you have the three keys, the wallet belongs to you (the hacker), and you can take it however you want.
Lao Gao said that the third signer was Bybit CEO Ben Zhou. When he signed, the information displayed on the screen on the cold wallet was not hackable like a computer. Logically speaking, if he looked carefully at the small screen, he might have noticed something unusual and not signed, and it would not have been stolen in the end:
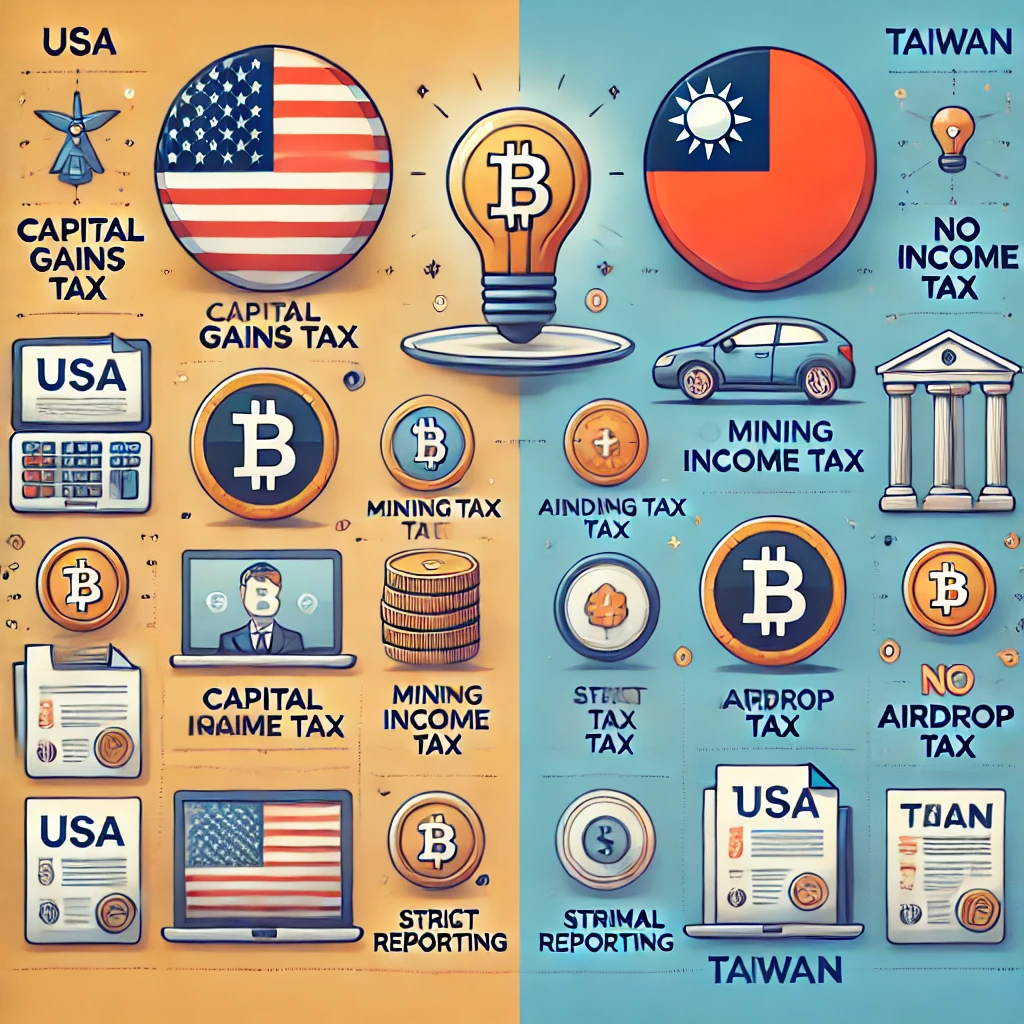
But why didn't he notice? It’s not his fault. This is also a drawback of virtual currency. The account of virtual currency is anonymous. Unlike our accounts, one account number and one name must match up, right? If you look at Zhang San and Li Si, you will know at a glance that the names are wrong, and you will find a problem.
Virtual currency is anonymous and only has an account number. And this account number is not a 6-digit number or an 8-digit number, but a long string of dozens of garbled numbers. Everyone is similar, so it is unrealistic to ask people to confirm one by one. They all look exactly the same.
Moreover, he often confirms this matter in this way, so he will not doubt that these two numbers are wrong, and then click to confirm. As a result, the top person in charge also clicked confirmation, and finally the funds were transferred out. If this matter is confirmed by AI, the problem may be smaller.
Information security experts pointed out that Lao Gao had a misunderstanding
However, security experts told Dongzhong that Lao Gao said that the disadvantage of cryptocurrency is that it is difficult to confirm transactions with garbled addresses. Bybit has three multi-signature people, everyone has the opportunity to check, Lao Gao may have misunderstood this matter, anti-theft SOP They all check whether there are extra transactions stuffed by gangsters, and then let the signer accidentally press confirmation:
In fact, the problem is that the multi-signature interface they signed in at the beginning is fake. Ben Zhou emphasized in the live broadcast that they had been confirmed, and the data on the Ledger was also confirmed (the same as the one initiated at the beginning).
By verifying the information on the cold wallet, you cannot know whether your transaction is related to social engineering hacking. This needs to be prevented from the beginning. This is also the first case of a multi-signature wallet being exploited, and it is not within the scope of prevention by just three people confirming the cold wallet information.
The expert pointed out that the Bybit theft incident prompted the industry to re-examine the security protection standards, that is, before initiating transactions, multi-signature initiators need to run a clean device and an SOP that eliminates the impact of social engineering to strengthen preventive measures and avoid similar tragedies from happening again.
*This article also attracted the wonderful insights of another security expert Huli. For more information, please see his Facebook post.